The Leading Governance, Risk, and Compliance Software
Build resiliency into your organization
Strategically manage risk, demonstrate compliance, and provide executives with visibility, assurance, and confidence. Reduce the cost of managing your GRC programs, save time, and prevent errors with a unified platform.
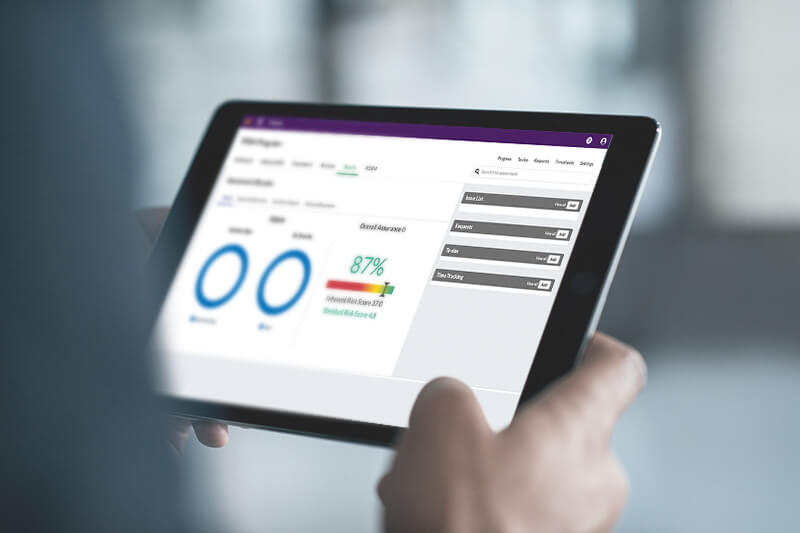
Manage your audit, risk, and compliance programs with efficiency and ease
With a sophisticated and integrated GRC program, you can quickly identify and mitigate risk and ensure compliance.
Streamline and automate critical workflows to increase your team’s collaboration, and deliver real-time insights to support low-effort, data-driven decision-making.
Get more from your GRC software
Get started quickly with pre-configured plug-and-play solutions designed to deliver best-in-class GRC programs. Gain deep insights with powerful analytics and striking storyboards.
Connect your essential tools in a unified platform to centralize and scale your work. Effortlessly deploy an intelligent GRC strategy with the help of our team of experts.
The first year we ran our projects [using HighBond], we identified about $14.7 million of risk items. [This] has gone down significantly to about $794,000, which is good for us—it means that, through our analytics, we’re able to enact changes within the processes.
Dior Silo, Compliance, Data Intelligence, and Analytics Manager, Coca-Cola